"Zero trust" is new architecture of "Network & Security" category, this movie is explaining about detail "What is Zero trust" & "HOW TO implement Zero trust architecture" into IT environment step by step.
Needs Creating a Secure Corporate Network that Supports Zero-Trust
Preparing for cyber threats with zero-trust networks and secure IT solutions

To meet our customers’ needs, we provide a wide variety of network services,
such as network connections between business locations and Internet connectivity,
as well as monitoring and operational services. We can support customers in adopting secure, zero-trust networks.
Does your organization have the following needs?
You want to
combine your closed network
with Internet access
for a solution that is optimal for your organization.
You have more locations than before and want to
limit the operational burden
related to WAN router management and reduce network circuit costs.
You want to be able to
comfortably use high-bandwidth applications
(such as video) and cloud-based applications.
You are concerned about
your company's security measures
as you proceed with implementing new-normal work styles.
KDDI Thailand has the answer

By automating IT asset management, Automatically check your device for vulnerabilities!
We centrally provide endpoint security such as IT asset management and detection of terminals violating security policies.

Security measures against "unknown threats"! Realize a secure PC terminal Minimize risks by blocking suspicious communications and processes
EDR can detect viruses and malware that are difficult to detect with antivirus alone. We will improve the detection accuracy at the terminal and realize "immediate response" to incidents.

Enhanced user authentication enables "correct" authority management for each user
Multi-factor authentication and restricted access (SSO) provide a highly convenient and secure environment for corporate cloud usage.

Safe and low-latency usage of the cloud services you need to boost work efficiency
As part of KDDI Managed zero-Trust, which promotes new ways of working for companies, we provide an integrated secure network environment that meets the challenges of global companies, such as remote work and mobile access.
What is zero-trust?
Learning Zero Trust definition by YouTube.
Zero-trust configuration example
We will propose the best solution for your environment.
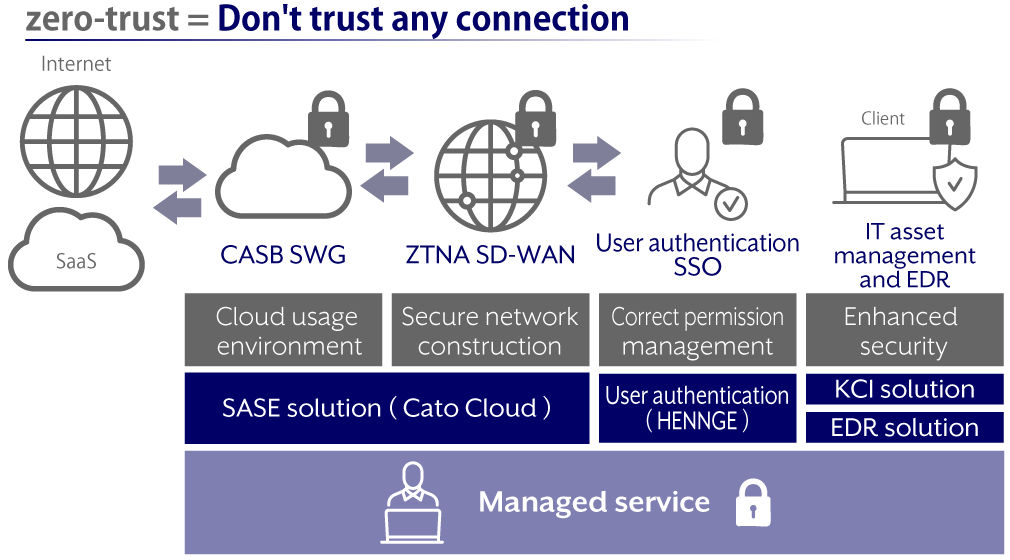
About Zero-trust
- Countermeasures that assume intrusions, as avoiding all indiscriminate attacks is difficult
- Strengthened security that detects threats after intrusion
- User authentication and infrastructure construction
- Standardized cloud usage, enabling location independence and high convenience
- Reliable security and usage guidelines for service providers
KDDI Zero Trust -Introduction-
Easy-to-understand explanation of the concepts behind Zero Trust by Yuki Wasai at KDDI Thailand. Download the free documentation now.
Related Resources








What is the best solution for your problem?
Please consult a KDDI consultant.